Given the recent spike in demand for employees to adopt remote working tools a lot of media attention has been generated regarding the topic. Start-ups have experienced a massive swing in fortunes and led economists and traders to shout from the mountaintops their virtues. More even-keeled folks have been asking about the security of these tools as well as ones that existed before the COVID-19 pandemic. One such tool is SharePoint, which has for the last several years been a great tool for promoting teamwork and collaboration across employees and teams. Current events have driven new interest and greater adoption in companies now forced to have employees work remotely. This article attempts to answer the question of how secure is the platform?
1. Things out of Owner’s Control

When using third-party software and platforms there are elements completely out of the control of the user regarding security. That being said, products like SharePoint developed by Microsoft do boast several advanced technologies to help secure the product from hackers. One such measure is the encryption protocols used, in the case of SharePoint AES-256 is used. Files are separated into chunks and then encrypted with its own key. These are then stored in what is termed “blobs” in various cloud storage accounts. These “blobs” are mapped, with their locations stored in a separate SQL server and the unique encryption key is also stored in a separate location. This is all done, and more, to secure data privacy and protection.
Large corporations can invest far more resources into developing a secure infrastructure when compared to a small to medium enterprise. To think that the SME can do the same is highly questionable. Major tech giants can provide high level and secure services. Often the end-user cannot change or modify core elements of the bigger infrastructure so these are out of their control. This leads the skeptical to question how secure their data is while been handled within the infrastructure. The simple answer is far more secure if the SME was forced to handle all their data themselves.
2. Education is Key
While skepticism is a valued trait when it comes to securing data, it is important to remember that we entrust other third-party applications with our data daily. Social media platforms and accounting software comes to mind. Not all of these applications apply the same encryption protocols. Accounting software, in general, will have higher standards to adhere to than some social media platforms. The point being made is that we share data on a continual basis understanding what we are willing to share and with whom is an important matter for consideration. Understanding what certain companies do or how they encrypt data to keep it secure is likewise an important consideration.
3. Things in the Owner’s Control

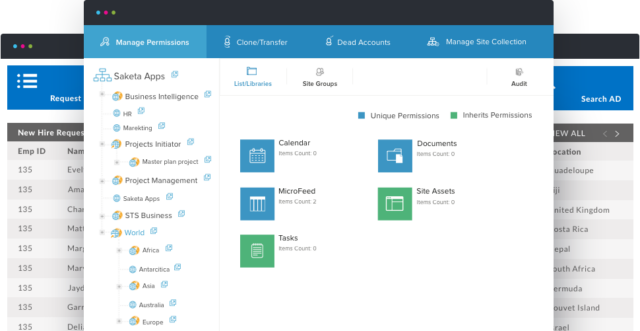
If the above section gave the impression that nothing is in the owner or end-users control then apologies need to be made. The truth is there are several things owners and end-users can do to increase their security posture when using tools like SharePoint. These measures, according to cipherpoint.com, include mostly steps to assure how secure your content is. These steps can and should include proper set up of external sharing; correct use of the OneSync client by laptop users, namely minimal use where possible; giving a high number of employees administrator privileges, and ensuring a high level of training for end-users which helps prevent initial compromises by attackers.
The above measures should form a unified security policy for the relevant enterprise. Adopting these measures can be a massive task in itself. Fortunately, there are security products that handle the securing and encryption of content before it enters Microsoft’s infrastructure if using SharePoint. This can be seen as an added level of security and given how prevalent data breaches and ransomware attacks have become this is never a bad thing. Another advantage presented by these security packages is the centralized policy handling of data. Requirements can be set and automated making policy adherence a certainty.
4. Think of Security as Layers

While third-party products such as those mentioned above can add an important layer of security that prevents hackers from performing side-channel attacks and intercepting data before it is encrypted. The importance of educating employees and providing high-level training cannot be underestimated. Hackers, scammers, and other cybercriminals are still very reliant on compromising accounts via social engineering. This more often than not requires the employee to act in a certain way by clicking a link or downloading a malicious attachment. If the compromise occurs at the source the attacker will not need to worry about breaking the encryption. These attacks are thoroughly preventable but do require employees to spot scams and phishing emails.
Conclusion
Once the term online is mentioned, security needs to be mentioned directly after. With companies relying more and more on remote workers, how they share and collaborate on projects needs to be viewed the same as securing the companies on-site infrastructure. While major tech giants do a lot in this regard there are still many owners and employees who can help ensure data privacy and protection.
The above measures are by no means an exhaustive list but rather show that there are things under the owner’s control as well as employees in securing data. By combining the infrastructure and security protocols of Microsoft, with third-party software, and a well-informed staff great strides are made in locking down important data vital to the continued success of the company. Data privacy is not just a consideration during the COVID-19 pandemic but rather as governments around the world look to pass data privacy laws, companies will increasingly need to comply with such laws. If failure to comply is found to be the case massive fines can be levied at the company. By applying some of the measures mentioned above great strides in compliance are made.